Protect the unprotected.
Your product team is in a race to migrate old apps to microservices.
New cloud-native apps are popping up with hundreds of potentially vulnerable APIs, but you don’t want security to be a bottleneck for developers. Traceable protects your apps from emerging and known threats, even as code and APIs change. It’s simple to deploy and automatically adapts to API changes to identify emerging threats, all without setting and updating static rules.
Get complete visibility into application security issues from end user to code for you and your developer colleagues.
What’s in it for you?
We know your job is beyond hard. Traceable AI can make it easier by protecting your apps and giving you the threat hunting tools and data you need to monitor, block, and investigate security threats.
Automatic API discovery and app topology
Real-time topology map shows API flows and interconnectivity between services (endpoints, internal, and 3rd party).
API Specifications offer more accurate specs than OpenAPI with real-time data from actual application usage.
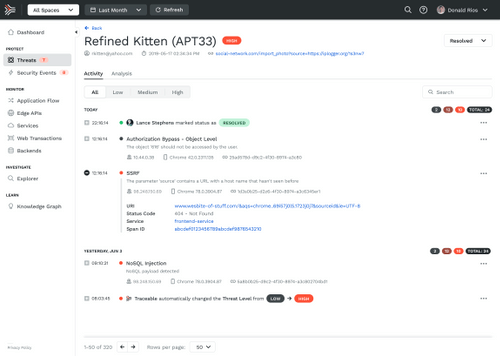
Protection from OWASP and emerging threats
TraceAI learns from application behavior to detect emerging threats based on application logic.
Built-in protection against OWASP Top 10, OWASP API Top 10, and other emerging threats.
User and behavior anomalies
Security events and business logic abuse mapped to users reduces false positives and lowers analysis & inference fatigue.
TraceAI identifies anomalous user behavior in the context of application usage and API interactions.
Granular data access visibility
Proactive data risk profiling automatically identifies high-risk assets and sensitive data.
Sensitive data is mapped to APIs for transparency into the services that access sensitive data.