Traceable Adds API Security Testing to it’s Platform
.webp)

Today, we are excited to announce API Security Testing! This addition to our API Security platform brings fully automated, closed-loop security testing to organizations’ APIs.We all remember the famous phrase of Andreessen Horowitz, “Software is eating the world”. It was definitely true at the time, but times have changed, yet again. APIs are now eating the world.Consider the Statistics…According to Gartner's latest Hype Cycle for APIs, 2022:
- 98% of organizations use or are planning to use internal APIs; up from 88% in 2019.
- 94% of organizations use or are planning to use public APIs provided by third-parties; up from 52% in 2019.
- 90% of organizations use or are planning to use private APIs provided by partners; up from 68% in 2019.
- 80% of organizations provide or are planning to provide publicly exposed APIs; up from 46% in 2019.
Using APIs to expose core business functionality and facilitate service-to-service communication has become standard practice. Not only do they give us several control points, but they also make it easier to contend with complex modern applications. As you can see from Gartner’s latest findings, the use of APIs is only accelerating.However, as we are becoming painfully aware, these modern API-driven applications come with their own issues like design complexity, visibility challenges, communication, and security, among many others. And part of an effective API security strategy requires incorporating API security testing, to find and fix vulnerabilities early in the software development lifecycle (SDLC). We can’t simply rely on finding vulnerabilities only in runtime.
What is API Security Testing and How Does it Work?
API security testing finds vulnerabilities in very early stages, giving developers and product security engineers more time and context to prioritize mitigation of vulnerabilities and build resilient systems. It’s typically a large part of Shift Left Security initiatives and integrated into DevOps workflows. For more details, download the API Security Testing datasheet.
API Security Testing for the Modern Enterprise: What Makes Traceable Different?
Traceable’s API Security Testing offering is built to make the testing of APIs fast, easy, and a seamless experience for both development and security teams. It supports organizations’ shift left initiatives, including providing remediation insights from runtime back to development, so developers can further harden their APIs. It is API focused providing complete vulnerability analysis that leverages functional testing, as well as API DNA and user attribution for improved detection and coverage. It offers extensive coverage for the OWASP API top 10, zero-day vulnerabilities, top CVEs (such as Java, Go, Node JS, AuthN, AuthZ, and many more), business logic vulnerabilities, and sensitive data exposure. Uniform API testing is based on dynamic payloads for standard tests, and dynamic Traceable payloads for business logic vulnerabilities such as BOLA – all with virtually zero false positives.Its DevSecOps focus enables companies to identify API security gaps between prod and pre-prod, perform fast scans for actionable results in CI/CD pipelines, scan at a granular level, from every build with API spec changes, and utilize integrations with application security tools, including SCA, SAST, DAST and IAST.
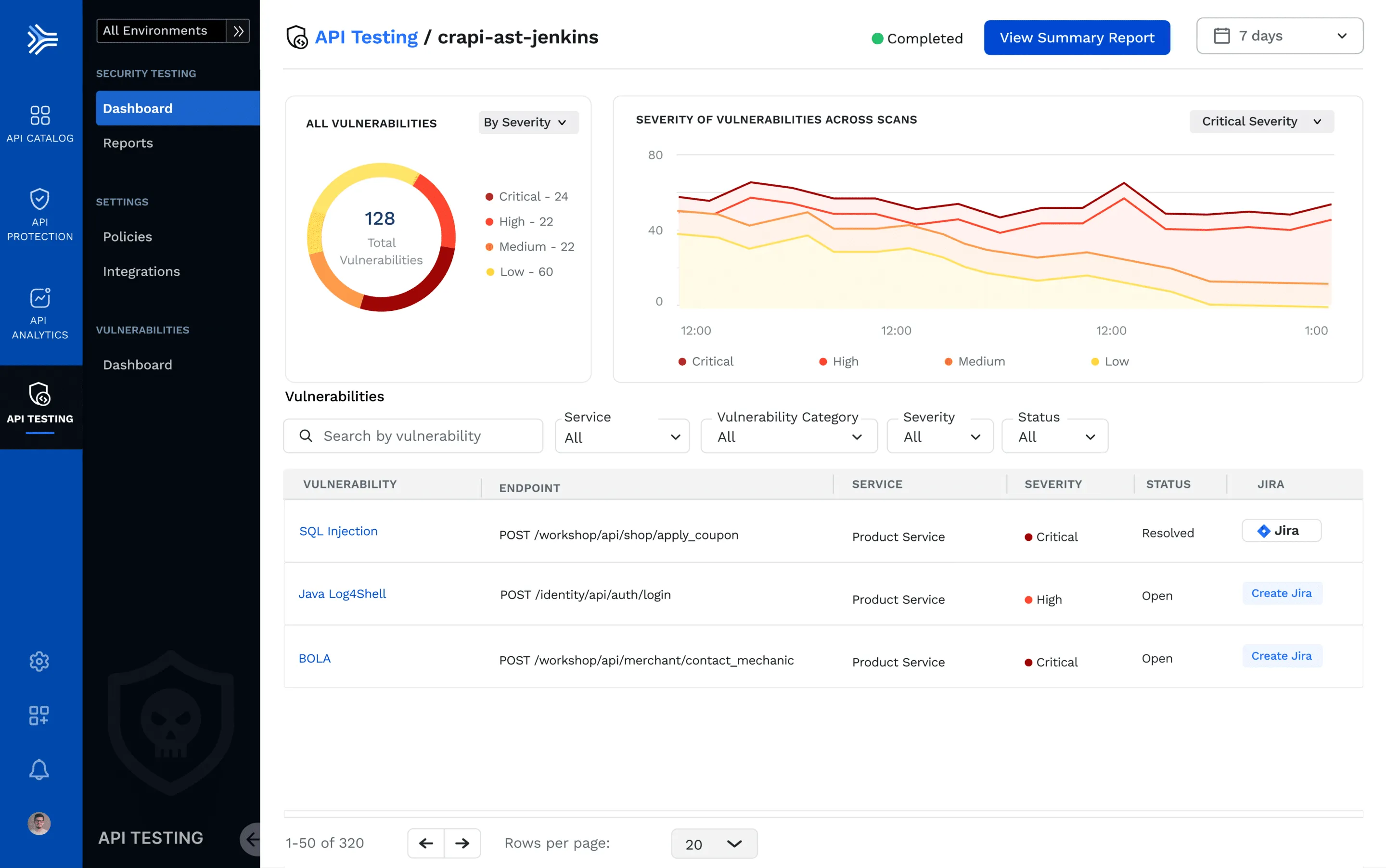
- Traceable Scans for What Matters: Traceable tests in real-time based on live traffic, with capabilities to generate and run tests on old traffic. It never generates tests for APIs that are inactive for a long time, or those that are never called. In other words, it is all about targeted testing on the active APIs with data that is close to actual parameters when the APIs are invoked at runtime. In addition, Traceable allows you to make pre-prod testing more efficient using production/runtime information.
- Operational Effectiveness: Traceable’s API security testing enables “closed loop” API security with numerous integrations (including CI/CD) for different teams, which make it easy to deploy into your environment with full automation. This reduces complexity often associated with API security and application security tooling.
- Eliminate Point AppSec Tools: Legacy AppSec tools such as DAST scanners don’t cover APIs. With Traceable, you get the complete API call flow when the vulnerability is detected, to be able to fix the issue correctly. Since Traceable’s API Catalog shows you the overall risk with regards to internet exposure, conformance and sensitive data flows, the vulnerabilities can be prioritized taking these important criteria into account.
- Reduce FTE Costs: It is typically more expensive to find software flaws in production vs. pre-prod. With Traceable, you’re able to reduce cost, from FTE and other resource-intensive activities, often associated with finding and fixing vulnerabilities in APIs, late in the Software Development Lifecycle (SDLC). While it’s true that only some vulnerabilities can be found in runtime, it’s important to incorporate a fully automated system to identify issues throughout the entire SDLC.
More of Traceable’s API Security Testing Features
Extensive security testing coverage for microservices and APIs.Extensive coverage for session-based anomalies, such as BOLA, Mass Assignment, and many others.Comprehensive coverage of API protocols - REST, GraphQL, SOAP, others.API mapping across environments and build versions of vulnerability correlation.Configurable vulnerability selections and payloads via plugins.Generate tests from live traffic, openAPI specs, recorded traces.Insertion into DevSecOps with scan initiation and vulnerability management.Risk-based prioritization using asset inventory, threat intel, and predictive modeling.Allows for virtual patching for exploits to shield while development creates the long-term fix.
One API Security Platform: Infinite Superpowers
Traceable discovers all of your APIs, and evaluates your API risk posture, stops API attacks that lead to incidents such as data exfiltration, and provides analytics for threat hunting and forensic research.
- API Security Testing: Eliminate the risk of vulnerable APIs in pre-prod, perform rapid scans that maintain speed of innovation, and automatically obtain remediation insights for developers to further harden their APIs.
- API Discovery and Governance: Automatic and Continuous API discovery that provides comprehensive visibility into all APIs, sensitive data flows, and risk posture – even as your environment changes.
- API Threat Protection: Automatically detect and stop known and unknown API attacks, business logic abuse attacks, as well as API abuse, fraud, and sensitive data exfiltration.
- Analytics and Threat Hunting: API Analytics from Traceable provides a rich set of security and application flow analytics in a data lake which can be used by security analysts to hunt for hidden IOCs.
About TraceableTraceable is the industry’s leading API security platform that identifies APIs, evaluates API risk posture, stops API attacks, and provides deep analytics for threat hunting and forensic research. With visual depictions of API paths at the core of its technology, its platform applies the power of distributed tracing and machine learning models for API security across the entire software development lifecycle. Book a demo today.-----------------References
- 2019 Gartner API Usage and Strategy Survey: This survey was conducted via an online survey from 30 July through 8 August 2019 with 112 Gartner Research Circle Members — a Gartner-managed panel.
- Hype Cycle for APIs, 2022; Published 10 August 2022 • ID G00770251 By Mark O'Neill, John Santoro: https://www.gartner.com/interactive/hc/4017511
The Inside Trace
Subscribe for expert insights on application security.
.avif)



